Introduction
In the preceding lesson we have mentioned that for the fulfilment of different goals, the IEEE 802 committee came up with a bunch of LAN standards collectively known as LANs as shown in Fig. We have already discussed CSMA/CD-based LAN proposed by the IEEE 802.3 subcommittee, commonly known as Ethernet. In this lesson we shall discuss Token bus, Token Ring based LANs proposed by the IEEE 802.4 and IEEE 8.2.5 subcommittees.

IEEE 802 Legacy LANs
Token Ring (IEEE 802.5)
Token Ring: A Brief History
Originally, IBM developed Token Ring network in the 1970s. It is still IBM’s primary local-area network (LAN) technology. The related IEEE 802.5 specification is almost identical to and completely compatible with IBM’s Token Ring network. In fact, the IEEE 802.5 specification was modelled after IBM Token Ring, and on the same lines. The term Token Ring is generally used to refer to both IBM’s Token Ring network and IEEE 802.5 networks.
Introduction
Before going into the details of the Token Ring protocol, let’s first discuss the motivation behind it. As already discussed, the medium access mechanism used by Ethernet (CSMA/CD) may results in collision. Nodes attempt to a number of times before they can actually transmit, and even when they start transmitting there are chances to encounter collisions and entire transmission need to be repeated. And all this become worse one the traffic is heavy i.e. all nodes have some data to transmit. Apart from this there is no way to predict either the occurrence of collision or delays produced by multiple stations attempting to capture the link at the same time. So all these problems with the Ethernet gives way to an alternate LAN technology, Token Ring.
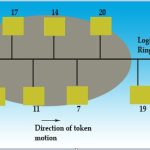
Token Ring and IEEE802.5 are based on token passing MAC protocol with ring topology. They resolve the uncertainty by giving each station a turn on by one. Each node takes turns sending the data; each station may transmit data during its turn. The technique that coordinates this turn mechanism is called Token passing; as a Token is passed in the network and the station that gets the token can only transmit. As one node transmits at a time, there is no chance of collision. We shall discuss the detailed operation in next section.
Stations are connected by point-to-point links using repeaters. Mainly these links are of shielded twisted-pair cables. The repeaters function in two basic modes: Listen mode, Transmit mode. A disadvantage of this topology is that it is vulnerable to link or station failure. But a few measures can be taken to take care of it.
Differences between Token Ring and IEEE 802.5
Both of these networks are basically compatible, although the specifications differ in some ways.
· IEEE 802.5 does not specify a topology, although virtually all IEEE 802.5 implementations are based on the star topology. While IBM’s Token Ring network explicitly specifies a star, with all end stations attached to a device called a MultiTaction Access Unit (MSAU).
· IEEE 802.5 does not specify a media type, although IBM Token Ring networks use twisted-pair wire.
· There are few differences in routing information field size of the two.
Token Ring Operation
Token-passing networks move a small frame, called a token, around the network. Possession of the token grants the right to transmit. If a node receiving the token has no information to send, it passes the token to the next end station. Each station can hold the token for a maximum period of time.
If a station possessing the token does have information to transmit, it seizes the token, alters 1 bit of the token (which turns the token into a start-of-frame sequence), appends the information that it wants to transmit, and sends this information to the next station on the ring. While the information frame is circling the ring, no token is on the network (unless the ring supports early token release), which means that other stations wanting to transmit must wait. Therefore, collisions cannot occur in Token Ring networks. If early token release is supported, a new token can be released immediately after a frame transmission is complete.
The information frame circulates around the ring until it reaches the intended destination station, which copies the information for further processing. The information frame makes a round trip and is finally removed when it reaches the sending station. The sending station can check the returning frame to see whether the frame was seen and subsequently copied by the destination station in error-free form. Then the sending station inserts a new free token on the ring, if it has finished transmission of its packets.
Unlike CSMA/CD networks (such as Ethernet), token-passing networks are deterministic, which means that it is possible to calculate the maximum time that will pass before any end station will be capable of transmitting. Token Ring networks are ideal for applications in which delay must be predictable and robust network operation is important.
Priority System
Token Ring networks use a sophisticated priority system that permits certain user designated, high-priority stations to use the network more frequently. Token Ring frames have two fields that control priority: the priority field and the reservation field.
Only stations with a priority equal to or higher than the priority value contained in a token can seize that token. After the token is seized and changed to an information frame, only stations with a priority value higher than that of the transmitting station can reserve the token for the next pass around the network. When the next token is generated, it includes the higher priority of the reserving station. Stations that raise a token’s priority level must reinstate the previous priority after their transmission is complete.
Ring Maintenance
There are two error conditions that could cause the token ring to break down. One is the lost token in which case there is no token the ring, the other is the busy token that circulates endlessly. To overcome these problems, the IEEE 802 standard specifies that one of the stations be designated as ‘active monitor’. The monitor detects the lost condition using a timer by time-out mechanism and recovers by using a new free token. To detect a circulating busy token, the monitor sets a ‘monitor bit’ to one on any passing busy token. If it detects a busy token with the monitor bit already set, it implies that the sending station has failed to remove its packet and recovers by changing the busy token to a free token. Other stations on the ring have the role of passive monitor. The primary job of these stations is to detect failure of the active monitor and assume the role of active monitor. A contention-resolution is used to determine which station to take over.
Physical Layer
The Token Ring uses shielded twisted pair of wire to establish point-point links between the adjacent stations. The baseband signalling uses differential Manchester encoding. To overcome the problem of cable break or network failure, which brings the entire network down, one suggested technique, is to use wiring concentrator as shown in Fig.

Star Connected Ring topology
It imposes the reliability in an elegant manner. Although logically the network remains as a ring, physically each station is connected to the wire center with two twisted pairs for 2-way communication. Inside the wire center, bypass relays are used to isolate a broken wire or a faulty station. This Topology is known as Star-Connected Ring.

Comments are closed